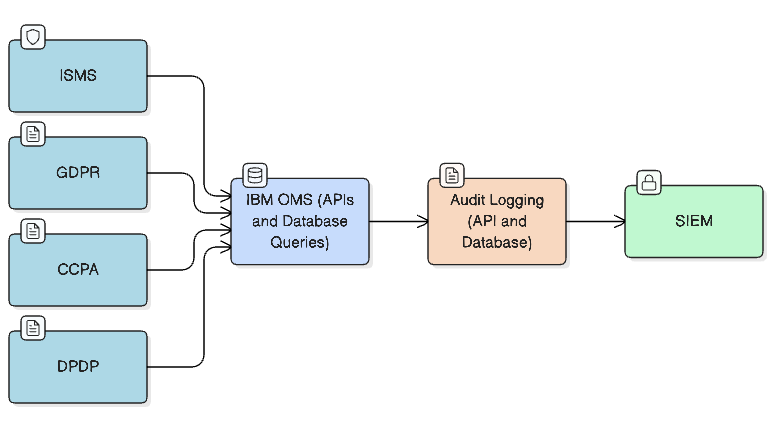
This solution supports a simple & dependable flow to track how customer information is accessed. This gives teams a clear view of who accessed what data, without adding load on day-to-day OMS operations.
Ensuring Data Privacy: End-to-End PII Access Logging in IBM OMS
Global Data Privacy Regulations: What Enterprises Must Comply With
As digital commerce expands across regions, enterprises must navigate a wide range of data privacy laws. Each country sets its own expectations on how customer information is collected, processed, accessed, and retained. For organizations running global ecommerce and omnichannel platforms, especially those handling PII in IBM OMS, understanding these requirements is essential.
To operate globally, enterprises must comply with multiple regulations that dictate how customer data can be used and who may access it.

Why Information Security Management System Compliance Matters for Order Management System (OMS)
Any OMS processes sensitive customer information such as names, phone numbers, email addresses, and sometimes payment-related data. Because of this, every OMS must ensure:
- Access transparency
- Controlled and authorized usage of customer data
- Secure audit logging
- Rapid breach detection
- Full traceability for compliance reviews
Different platforms approach this differently. This article focuses on how IBM Sterling OMS supports ISMS-aligned controls and PII access visibility.
A centralized PII logging framework is not yet a universal ISMS requirement. It is currently emphasized in markets such as Korea, but as more countries align with ISO-27001, similar expectations are likely to emerge globally.
For enterprises using IBM OMS, this translates into the need for a robust audit mechanism that records when sensitive data was accessed, who accessed it, and which fields were retrieved.
Regulations such as GDPR (Europe), CCPA (US), ISMS (Korea), and DPDP (India) require enterprises to maintain transparent and tamper-proof audit trails. Failing to do so can lead to penalties, loss of customer trust, and barriers to operating in regulated markets.
Since IBM OMS frequently processes customer names, addresses, and contact details, a consistent and traceable logging framework is essential for both API and database access.
All API calls that read or return customer information are tracked. The framework identifies when PII is involved and records:
- Who initiated the request
- The channel used (OrderHub, Call Center, mobile app, website, integrations)
- The type of customer data accessed
The same level of visibility is applied to database activity. When a user or service runs a query on customer-related tables, the framework captures:
- Who executed the query
- When it was run
- What customer information was retrieved
This removes a common audit blind spot and supports markets where PII access logging is mandatory.
Every log includes the basic information an auditor or security team would need, such as the user, timestamp, source application, and the part of the customer record that was accessed. This makes it much easier to answer questions during compliance reviews.
Log collection does not interrupt OMS transactions. Events are processed separately and stored in secure cloud storage. This keeps the system responsive even during peak order volumes.
The stored logs are forwarded to security platforms such as Google Chronicle SecOps, Splunk, IBM QRadar, and many others. These tools help teams:
- Monitor access patterns
- Detect unusual or excessive access
- Conduct audits efficiently
The framework is designed to avoid any impact on OMS performance. Logging uses lightweight filters that add negligible overhead to API and database operations. Processing occurs outside the OMS JVM to prevent spikes in memory or CPU usage.
Because the architecture is fully decoupled and asynchronous, OMS can handle high workloads without affecting SLAs. Compliance logging remains invisible to users while maintaining operational stability.
- A call center agent views the customer address → captured as an API log
- Mobile app retrieves order details → logged with source & PII fields
- DBA runs SQL on YFS_PERSON_INFO → logged with SQL text & tables
- Security team detects abnormal access volume → SIEM sends alert
Governance & Monitoring Recommendations
To maximize compliance:
- Review SIEM dashboards weekly
- Set alerts for unusual access patterns
- Conduct quarterly access audits
- Enforce identity-based access policies
- Validate cloud storage access control (IAM)
Good governance strengthens both compliance and internal security posture
Key Benefits
Audit Readiness
Centralized logs simplify ISMS audits and regulatory reviews.

Full-Stack Visibility
Covers both OMS APIs and direct DB queries, eliminating blind spots.

Zero Performance Impact
Asynchronous processing ensures no slowdown in order workflows

Cloud-Native Security
Logs stored with IAM policies, encryption, and firewall-controlled access.

Scalable Across Regions
Framework supports GDPR, CCPA, DPDP, and global expansion.
Author Details

Sureesh Deenadayalan
Solution Architect
Over 13 years of experience in IBM Sterling OMS, foundation, next-generation call center, and store Apps, upgrades and cloud migration. Have designed end-to-end order management, sourcing, and post-purchase workflows for large-scale retail systems.